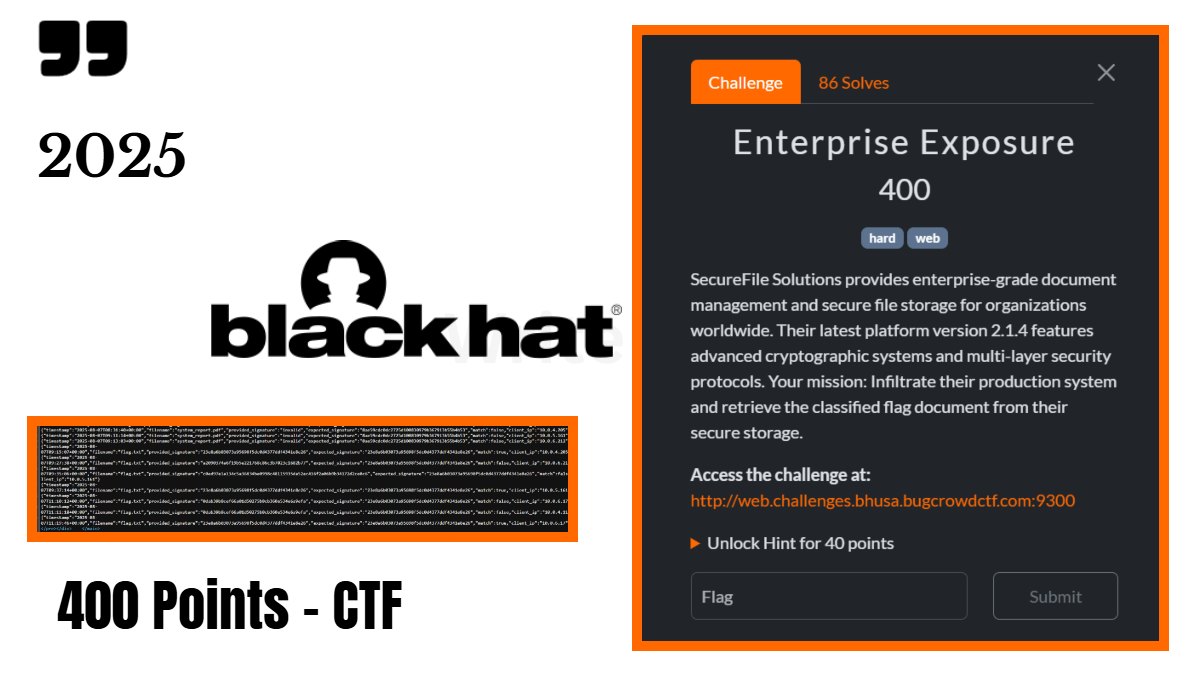
The Challenge description was – “SecureFile Solutions provides enterprise-grade document management and secure file storage for organizations worldwide. Their latest platform version 2.1.4 features advanced cryptographic systems and multi-layer security protocols. Your mission: Infiltrate their production system and retrieve the classified flag document from their secure storage.”
This was the hard challenge under web category. When visiting the page we found an API end point url – “/api&endpoint=status” this endpoint contained raw JSON embedded in HTML:
“endpoints”: { “legacy_api”: “api\/legacy\/bridge.php”, “crypto_validator”: “api\/internal\/crypto_validator.php”, “file_handler”: “core\/file_handler.php”, “admin_interface”: “modules\/admin_interface.php” }
This confirmed enpoint inclusion.
Bridge.php contained legacy HMAC Validator for data input and signature. And also hardcoded the list of legacy HMAC keys and it pointed to the new system with the hint “core\/file_handler.php”.
Crypto_validator.php this is where the crypto logic is. It derives the key from a secret_input, by doing
- reverse input
- XOR with 0x42
- take first 16 bytes
- md5 it
- take first 8 chars → derived key
Then the system signs flag.txt using:
hash_hmac(‘sha1’, ‘flag.txt’, dervied_key)
So we need to find the base secret that produces a valid key.
Trigger Key Drivation Logging To Get The Valid Signature
So now we triggered using different secrets like:
http://web.challenges.bhusa.bugcrowdctf.com:9300/?page=api/internal/crypto_validator.php&debug=crypto&secret=admin
The system logged every attempt here – “/logs/crypto_validation.log“
“http://web.challenges.bhusa.bugcrowdctf.com:9300/?page=logs/crypto_validation.log“, we used LFI vulnerability to read the file’s content directly
The log file we’ve obtained is the final piece of the puzzle! for sure. It contained a checksum for a file that was processed by this system – /crypto_validator.php
Now I sent the request to file_handler.php with the correct filename (flag.txt) and with a fake signature.
“http://web.challenges.bhusa.bugcrowdctf.com:9300/?page=core/file_handler.php&file=flag.txt&sig=123”
This will trigger the validsignature function, also log the attempt and the correct signature to the file system.
Step 2 – Reading the log File (Black Hat USA 2025)
“http://web.challenges.bhusa.bugcrowdctf.com:9300/?page=logs/file_access.log”
Inside the log we found out the JSON entry containing both provided_signature and expected_signature
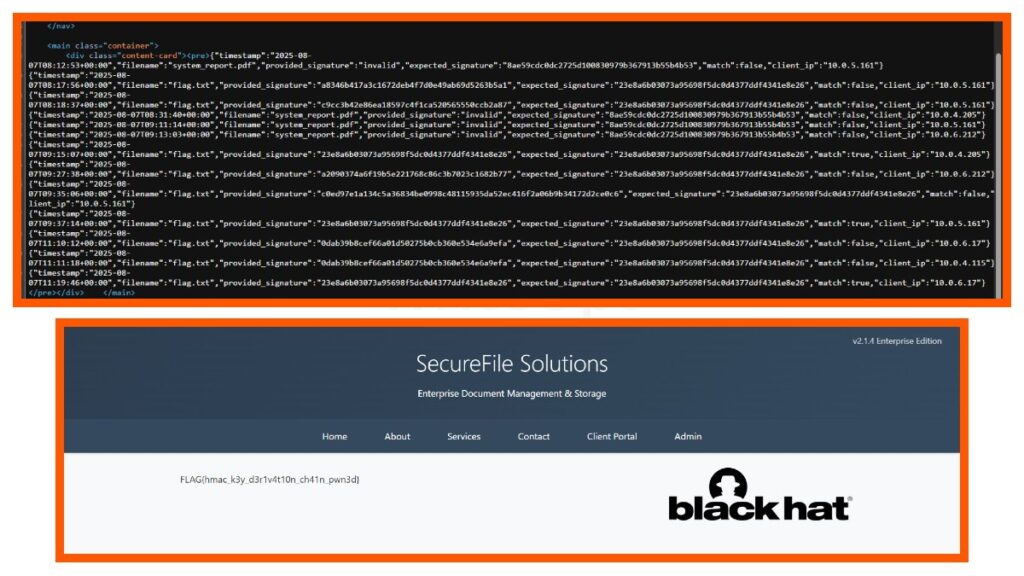
Based on the log data the correct signature for flag.txt is:
“23e8a6b03073a95698f5dc0d4377ddf4341e8e26”
And this was the correct HMAC signature to access the flag.txt
This simple request with the signature gave me the flag on the page:
“http://web.challenges.bhusa.bugcrowdctf.com:9300/?page=download&file=flag.txt&sig=23e8a6b03073a95698f5dc0d4377ddf4341e8e26”
After submitting it passed the server-side-validation and returned the flag content.