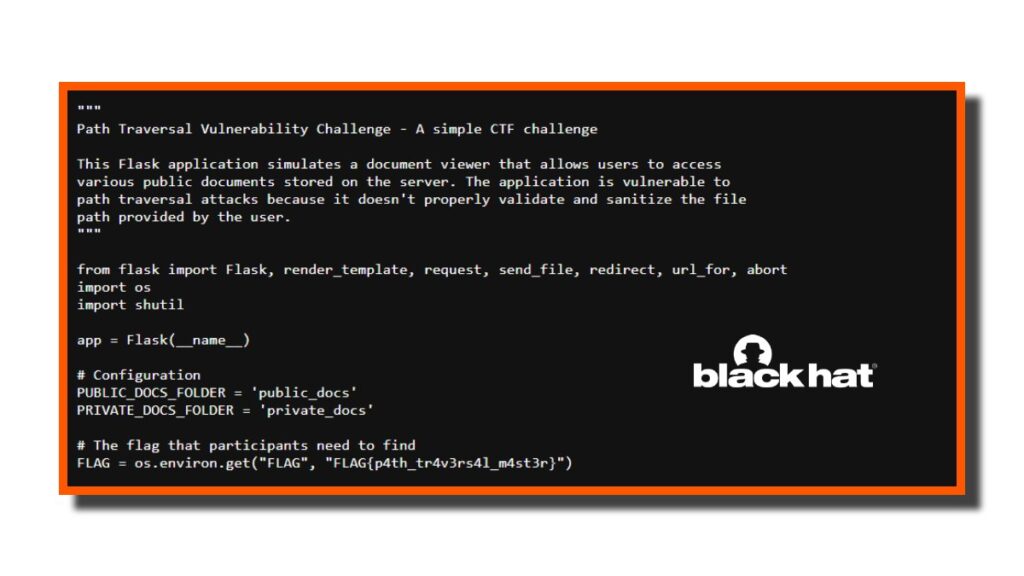
Blackhat USA 2025, Challenge Description was – “You’ve discovered a simple document viewer application called “DocView” that allows users to access various public documents stored on the server. Can you find a way to access the hidden flag?”
As the challenge name says a step back to leap forward is a strong hint that we can use path traversal or directory traversal to move one step up using “../”
The application named DocView likely takes a filename as a parameter “/view?file=welcome.txt” So if the server doesn’t sanitize the input, allowing us to move one step above the current directory. Using character sequences like “../”
The About-Us page says that:
“All public documents are stored in the public_docs directory”
“The Page also meantioned that the application is built using with the python flask framework. Typically in flash step up, the main application file will be located in the root directory and is often named as app.py or main.py”
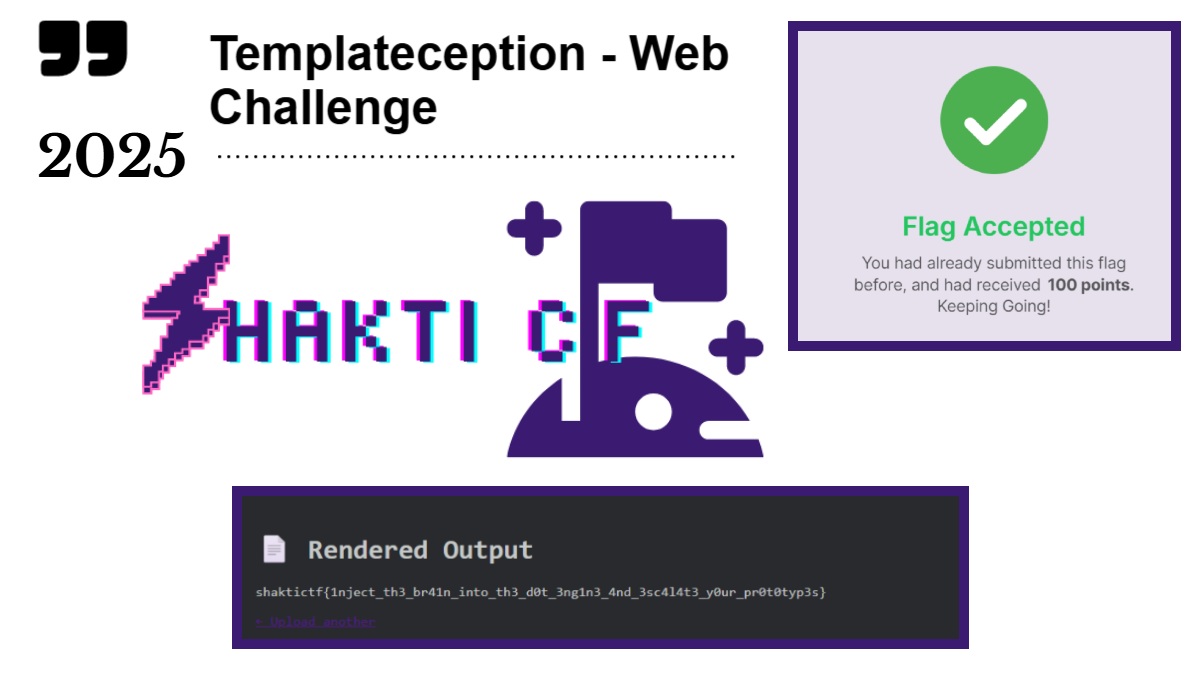
Step 2 – Directory Traveral Payload – (Blackhat USA 2025)
“http://web.challenges.bhusa.bugcrowdctf.com:9092/view?file=../app.py”
Using this payload, It tells the server don’t give me a file from the /view folder instead go one step above the current directory from public_docs to the root application in the web server, where the app.py file was located. and we got the flag which was hardcoded on the file.