Black Hat USA 2025 CTF, The challenge description was – “Welcome to our newly modernized authentication system! We’ve successfully ported our legacy PHP API to Python Flask while maintaining full backward compatibility with our existing authentication mechanisms.
Our development team has thoroughly tested the migration and ensured that all existing authentication flows continue to work exactly as they did in the original PHP system”
The challenge was likely PHP loose comparision vulnerability also called “Magic Hash” The description says the Python application use PHP style comparision.
When the backend system compares 2 strings using (==) operator:
if ($_POST[‘password’] == $stored_hash)
$stored_hash can be vulnerable if it is like “0e123456“
In PHP when you compare a string with an integer using the == operator, PHP “type juggling” converts the string to the number.
If the logic behind the scene, Thing MD5 hash starts with 0e followed by only digits, PHP treats it as 0 in a comparison.
“0e123” == “0e456” // This will become true
Step 2 – Finding the MD5 Hash That Begins With 0e
Common hashes:
- s878926199a -> md5(‘s878926199a’) = 0e545993274
- s1502120010a -> md5(‘s1502120010a’) = 0e830400451
- 240610708 -> md5(‘240610708’) = 0e462097479
- s214902148 -> md5(‘s214902148’) = 0e84865181
The challenge explicilty said the format for the login POST request, a JSON body with username and password. I tried username as admin and password as one of the magic hash string “s878926199a“.
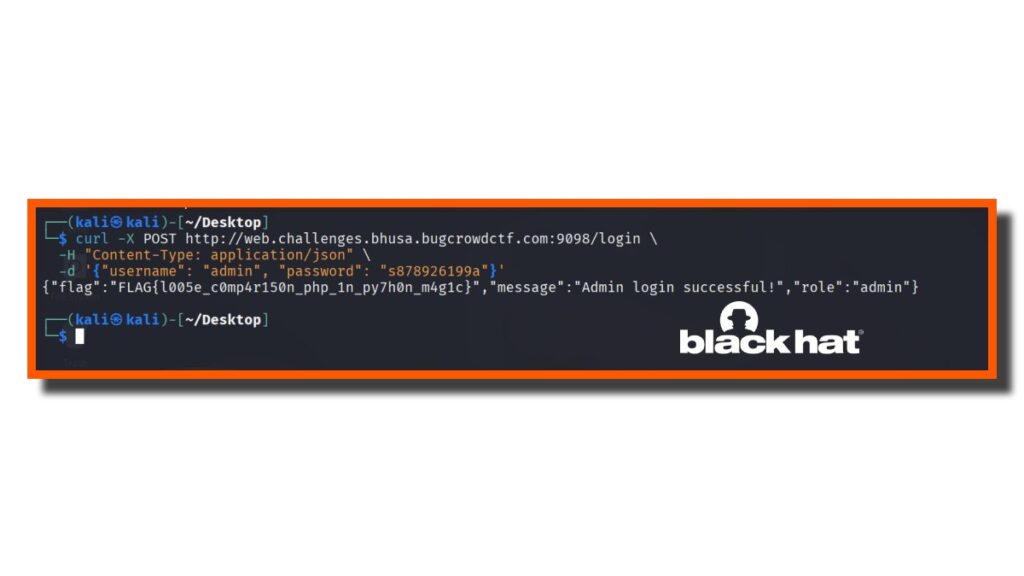
Now the python flash processed the password and compared it with the stored_hash using == operator. Since both had scientific notation interpretation result became true and got the flag.